Any Zip Password Recovery: Cracking the Code
Have you ever been locked out of your own zip file? It's incredibly frustrating to know that important data is just a password away, especially if you're dealing with any zip password recovery. Don't worry, you're not alone. This article will guide you through various methods to regain access to your precious files.
Understanding Zip Files and Encryption
Before we dive into recovery methods, let's briefly understand what we're dealing with. Zip files are like digital suitcases, compressing multiple files into one neat package. They're often used for sharing, archiving, or simply saving space.
The problem arises when these suitcases get locked with a password. Zip files use encryption algorithms to protect your data, making it impossible to access without the correct key. The stronger the encryption, the harder it is to crack.
Any Zip Password Recovery: Methods That Work
The best approach for any zip password recovery depends on factors like the password's complexity and your technical expertise. Here are some proven methods:
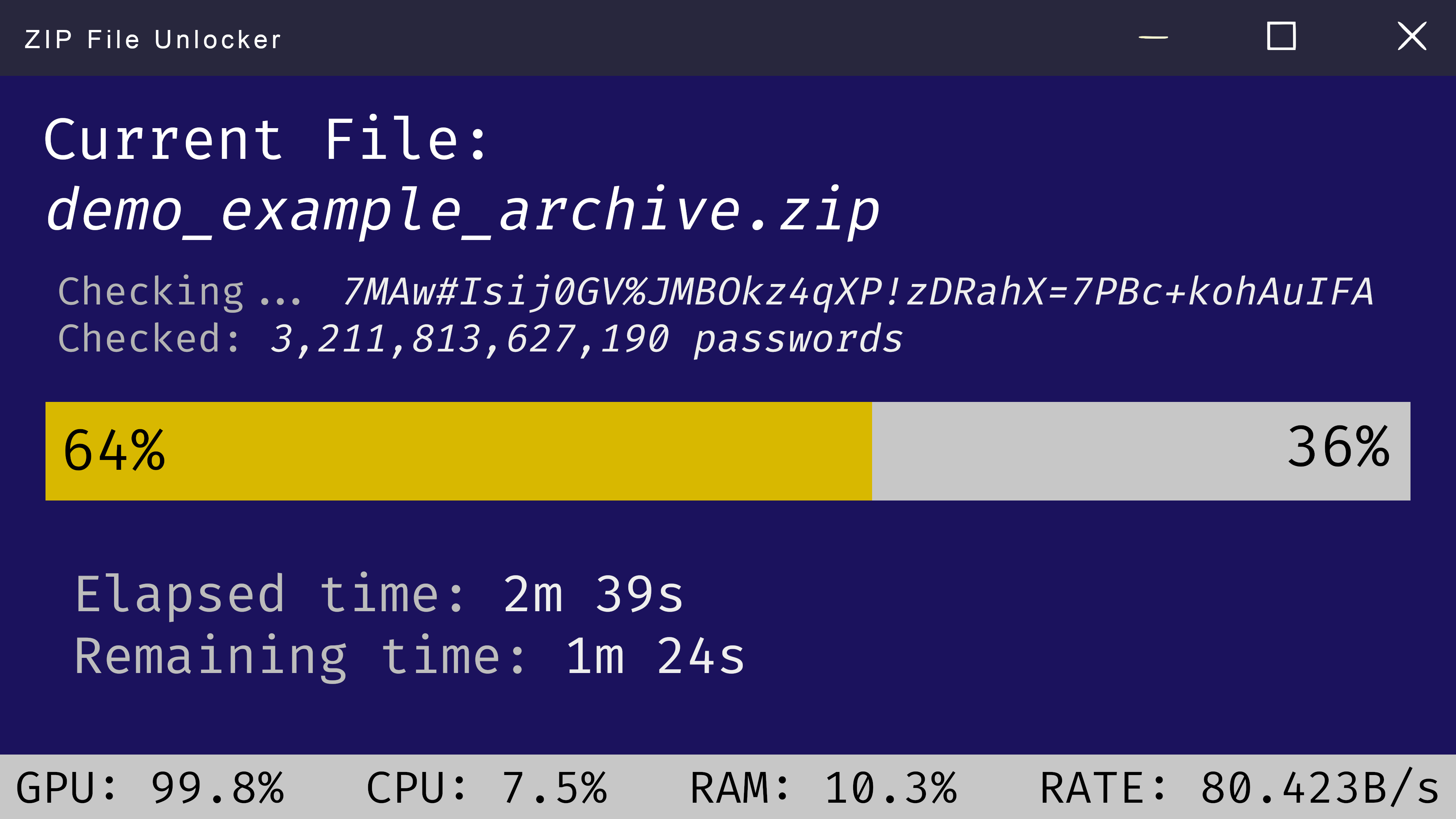
1. Brute-Force Attacks
As the name suggests, brute-force involves trying every possible combination of characters until the correct password is found. While effective, it can be time-consuming, especially for complex passwords.
Several software tools specialize in brute-force attacks on zip files. These tools often offer different attack modes, including dictionary attacks (using pre-compiled word lists) and brute-force attacks with customizable character sets.
Pros:
- Potentially effective for any password
- Various software tools available
Cons:
- Can be extremely time-consuming
- May not be successful for very complex passwords
2. Dictionary Attacks
If you suspect the password uses common words or phrases, dictionary attacks are a good starting point. These attacks use pre-compiled lists of words and variations, drastically reducing the time compared to pure brute-force.
Pros:
- Faster than pure brute-force
- Effective for passwords based on common words
Cons:
- Ineffective for strong, randomly generated passwords
3. Password Recovery Software
Several dedicated software solutions are designed specifically for any zip password recovery. These tools often combine multiple attack methods, including brute-force, dictionary attacks, and more sophisticated techniques.
Popular Zip Password Recovery Software:
- PassMaster: Known for its user-friendly interface and comprehensive features.
- Zip Password Cracker Pro: Offers advanced customization options and supports various encryption algorithms.
- John the Ripper: A powerful, open-source password cracking tool that also supports zip files.
Choosing the Right Software:
When selecting software, consider factors like ease of use, supported encryption algorithms, attack modes, and your budget (some tools offer free trials or limited functionality).
4. Online Password Recovery Services
If you're uncomfortable with using software or lack the technical expertise, online password recovery services offer a convenient alternative. These services typically utilize powerful remote servers to crack passwords, potentially reducing the recovery time.
Caution: Always choose reputable online services and be wary of potential scams. Ensure they have a secure website and clear privacy policies.
Tips to Enhance Password Security
While recovering a lost password is crucial, preventing such situations in the future is equally important. Here are some tips to enhance your password security:
- Use Strong Passwords: Combine uppercase, lowercase, numbers, and symbols. Aim for at least 12 characters.
- Don't Reuse Passwords: Avoid using the same password for multiple accounts.
- Enable Two-Factor Authentication: Add an extra layer of security to your accounts whenever possible.
- Consider a Password Manager: These tools securely store and generate strong passwords for all your accounts.
Conclusion
Losing access to your zip files can be a stressful experience. However, with the right approach and tools, any zip password recovery is possible. Remember to choose the method that best suits your situation and prioritize strong password practices in the future.
Recover your data, but more importantly, protect it proactively.
 Windows
Windows MacOS
MacOS Linux
Linux